Key insights from the OpenText Cybersecurity 2026 Threat Report
Explore expert perspectives, practical guidance, and cybersecurity insights from the OpenText Cybersecurity community.
Tyler Moffitt
April 14, 2026

Cyber threats are not just increasing. They are changing shape.
The latest OpenText Cybersecurity Threat Report, based on telemetry from tens of millions of endpoints across business and consumer environments, reveals a shift that many organizations are still not fully accounting for.
Attackers are moving faster, personalizing more effectively, and increasingly targeting identity over traditional vulnerabilities.
Here are the key insights you need to know.
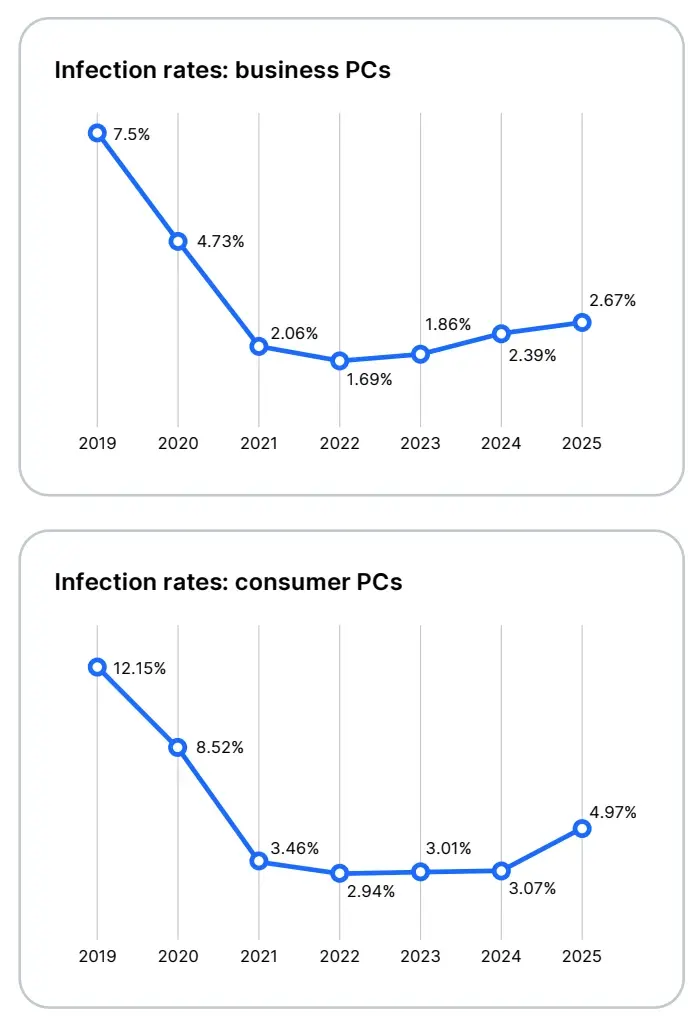
1. Business and consumer threats are moving in different directions
One of the clearest signals in this year’s data is that business and consumer environments are no longer moving in parallel. They are diverging.
Consumer infection rates surged by over 60% year-over-year, while business environments saw a more modest increase of around 11–12%.
At first glance, that might suggest businesses are better protected. They’re not. Attackers are simply being more selective.
In consumer environments, scale wins. High-volume campaigns, broad targeting, and repetition drive results. In business environments, attackers optimize for impact by targeting identities, gaining access, and expanding from there.
- Consumers are hit with high-volume, opportunistic attacks
- Businesses face fewer attacks, but far more targeted and damaging ones
This split is critical. It shows attackers are optimizing for scale in consumer environments and precision in business environments.
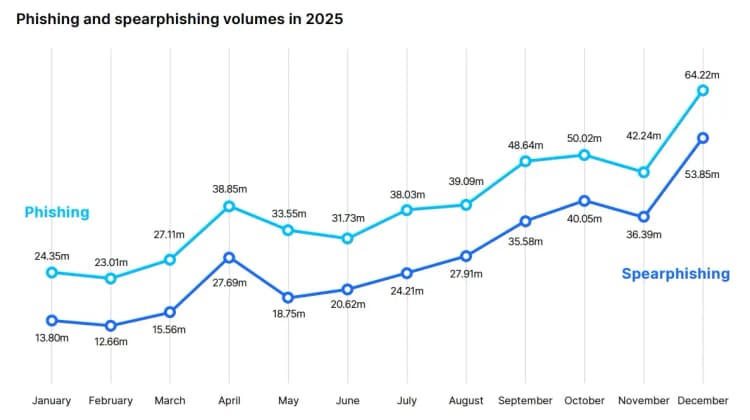
2. Identity has become the primary attack surface
The biggest shift in the threat landscape is not malware. It is identity. Attackers are no longer forcing their way in.
They are logging in.
Phishing has evolved into one of the most effective entry points, driven not just by AI-assisted personalization, but by how easy it has become to profile targets at scale. The data people share publicly on social media, professional platforms, and across the web gives attackers everything they need to build convincing, highly contextual lures.
AI accelerates that process.
What used to take time and effort can now be automated:
- Personal details can be scraped and assembled instantly
- Messaging can be tailored to roles, habits, and relationships
- Campaigns can be generated and iterated in real time
The result is phishing that feels familiar, relevant, and legitimate.
- Spear phishing now represents the majority of phishing activity
- Credential theft has become the fastest path to access
- Attacks are designed to blend in, not stand out
This is why traditional awareness of “suspicious emails” is no longer enough.
The modern attack doesn’t look suspicious. It looks routine.
3. The downloads folder has become a primary infection vector
One of the more telling findings in the data is where infections are actually occurring.
The Downloads folder is now a primary infection vector, especially in business environments.
Users are not being hacked. They are being convinced.
Files are delivered through trusted channels like email or collaboration tools, and execution is initiated by the user. That means many traditional defenses are bypassed by design.
- A significant share of business infections now originate in Downloads
- Delivery often happens through legitimate workflows
- Execution depends on user action, not exploitation
This is not a vulnerability problem. It’s a behavior problem. And that requires a different approach to defense.

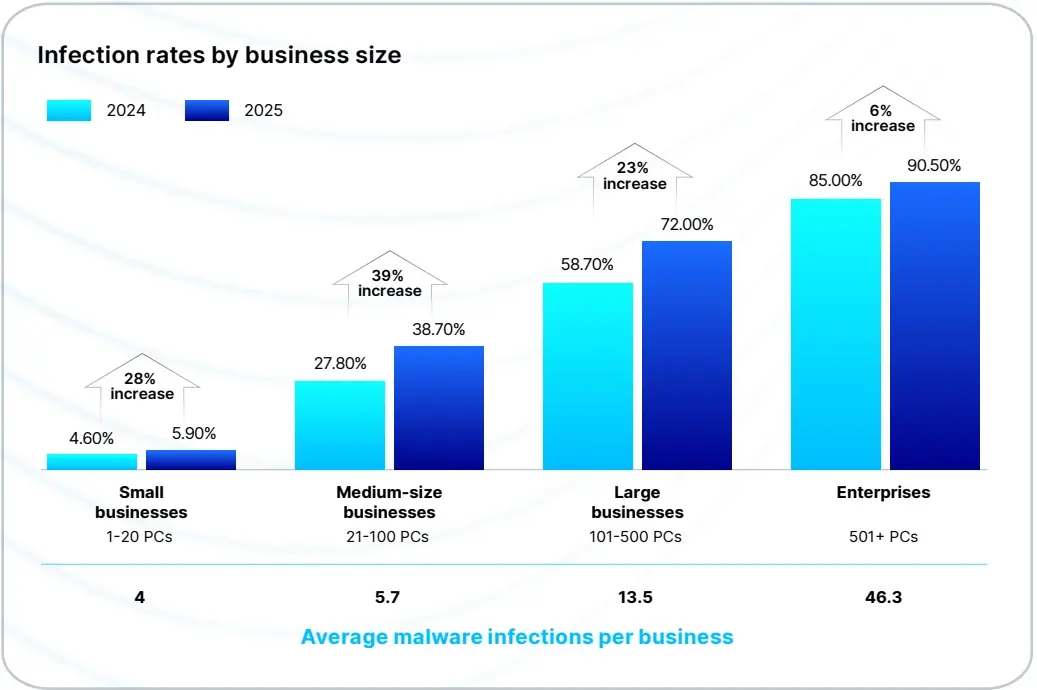
4. SMBs are seeing the fastest growth in threat exposure
Small and mid-sized businesses are no longer under the radar. They are being actively targeted, and that targeting is accelerating.
SMBs experienced a 39% increase in malware encounters year-over-year, one of the fastest growth rates across any segment.
This is intentional.
SMBs often operate with fewer resources, less layered security, and a heavier reliance on identity-driven workflows. That makes them easier to access and harder to defend once compromised.
At the same time, enterprise exposure remains high.
Over 90% of endpoints in very large organizations encountered malware, reflecting constant pressure at scale.
But the key difference is trajectory. Enterprises are managing persistent exposure. SMBs are seeing rapid growth in targeting and success rates.
Attackers are no longer choosing between volume and impact. They are getting both.
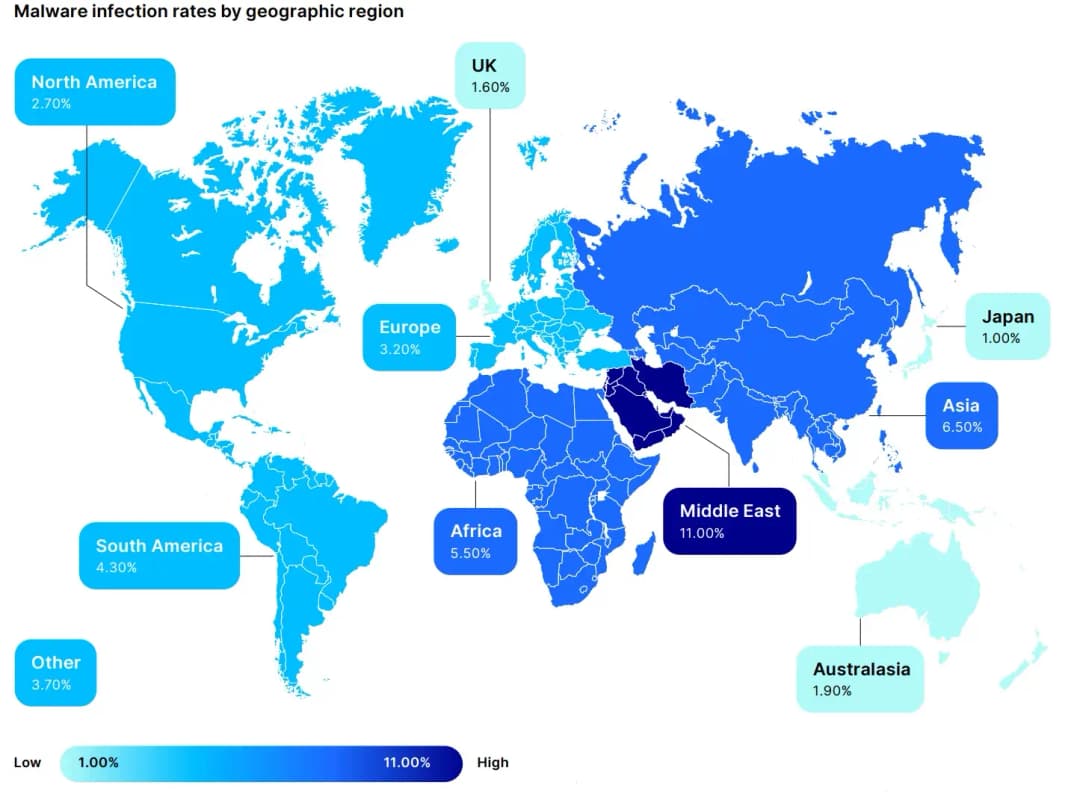
5. Geography still plays a major role in risk
Threat activity is not evenly distributed, and the differences are not subtle.
Some regions consistently experience significantly higher infection rates, and it is not just because attackers are targeting them more aggressively. It is because the conditions make attacks easier to succeed.
The Middle East stands out as one of the highest-risk regions, with Africa and parts of Asia also showing elevated exposure compared to global averages.
The common factor is environment. In many of these regions, out-of-date and end-of-life operating systems are still widely in use. Patch cycles are inconsistent, and known vulnerabilities remain exposed for longer periods of time.
In those conditions, attackers don’t need advanced techniques. Basic, well-known exploits are often enough.
- Legacy systems remain active
- Patching is inconsistent
- Vulnerabilities persist longer in the wild
That changes the equation. The pool of exploits that can bypass outdated operating systems only grows over time, it never shrinks. Risk is no longer just about who is being targeted, it is about where defenses are weakest.
6. Layered security is what actually reduces risk
Security is not about a single control. It is about how controls work together.
The data continues to show that layered approaches reduce infection rates, especially when combining multiple types of protection.
- Endpoint protection helps detect and block threats
- DNS filtering reduces exposure to malicious infrastructure and phishing sites
- Security awareness training addresses the human element
Individually, each layer helps. Together, they close the gaps attackers rely on. The challenge is that many organizations still deploy these controls in isolation.
Attackers only need one gap. Defenders need to close as many as possible.
Where defenders are still falling behind
Many organizations are still aligned to outdated assumptions about how attacks happen. Too much focus remains on ransomware, while initial access vectors like phishing and credential theft continue to drive the majority of compromises. Backup is often treated as a complete strategy, even though it does nothing to prevent access in the first place. And in many cases, identity risk is still underestimated.
Attackers are not standing still. They are adapting quickly to what works. Defenders need to do the same.
Cybersecurity outlook 2026
The direction of the threat landscape is clear. Identity will remain the primary battleground. Social engineering will continue to outperform exploitation. Malware will become more fragmented and harder to track. Attack chains will continue to accelerate.
Organizations that recognize these shifts can adapt. Those that don’t will continue reacting to attacks instead of preventing them.
Download a copy of the OpenText Cybersecurity 2026 Threat Report

Tyler Moffitt
Tyler Moffitt is a senior threat research analyst who stays deeply immersed within the world of malware and antimalware. He is focused on improving the customer experience through his work directly with malware samples, creating antimalware intelligence, writing blogs, and testing in-house tools.